Now more than ever your organisation needs to be prepared for the very real risk of cyber-attacks.
In this blog, I’ll be discussing the lessons we can learn from the Log4j vulnerability and how your organisation can get assurances in managing risks and protect itself from a major cyber-attack like this by being part of Housemark’s Information Security Forum.
There is an XCD cartoon which I really like, and it became quite true before Christmas:
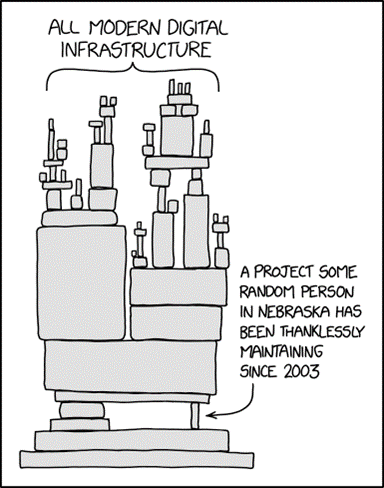
I am talking about the vulnerability in the Log4j software which is probably unfair to describe as a project maintained by a random person in Nebraska but it’s certainly a key component of the modern digital infrastructure. This security incident was discovered and reported by an engineer of the Chinese e-commerce retailer Alibaba on the 9th of December and very quickly the realisation that this was a major threat spread like wildfire across the cybersecurity community.
As always, one of the first challenges was how to explain the issue to non-technical people. How to describe the threat and scale of the problem in simple words which could justify the resources needed over the next few weeks to fix or mitigate the issue. As always, Twitter produced the best answer:

There were some creative alternatives which point to the fact that you probably don’t know where this vulnerability may be located.

However humorous and creative these explanations are, the risk is very real with some experts defining this issue as the biggest security vulnerability in history and one that will haunt the internet for years. The National Cyber Security Centre (NCSC), produced clear and concise management explainers including one for board members and detailed technical guides.
The Log4j vulnerability is a perfect example of how difficult it is for organisations to achieve some level of assurance that they are managing the risk from cyberattacks. A lot has been written about the asymmetric nature of cybersecurity threats, and it is a recognised fact that most modern businesses with internet connectivity and presence are constantly under attack from a wide variety of motivated, creative, and adaptive adversaries that work together forming what can only be described as a supply chain of cyber-crime.
One of the key strategies to deal with such an environment is to share intelligence and to collaborate. This is what Housemark’s Information Security Forum have been doing since late 2018. Formed as the Warning Advice and Response Point (WARP), for the social housing sector in the UK and supported by the NCSC, the group has over 20 members ranging from large G15 organisations to specialist care providers and ALMOs.
Even though the Log4j incident ruined a lot of people’s run up to Christmas, members of Housemark’s Information Security Forum worked together to identify the attacks, warn each other of issues they were experiencing and looked for potential solutions.
Over the last few years, members of the forum have been able to share invaluable intelligence on security incidents and threats, such as Log4j, but also on products and how to get the most out of them and most importantly, what works and what doesn’t when implementing security controls, rolling out awareness campaigns and communicating with senior leaders. The value of being able to learn from others, ask questions and access the wisdom of the crowd in a safe environment with high trust is something unique to this group.
With the level of trust built over the years, we can challenge ourselves and aim to improve together. An example of this is the work we have done on email security where we have created a league table of members and worked together to improve the standard of email security across the group. Very often, members of the group report that they’ve been given the green light to make a change or implement control in their organisation because the Forum recommended the approach and others in the group have done it successfully. I cannot think of a better way to spread best practice in an environment where working alone does not pay off.
The next time the execs in your organisation ask you about the latest security threat, don’t send them a clever tweet to explain it, tell them you discussed it at Housemark’s Information Security Forum and colleagues there recommended a series of actions which other organisations in the group have successfully tested and implemented. If you want to experience what it’s like to join a group of cyber security and data protection professionals in the sector, get in touch.
Our next meeting is on the 9/10 February, online. Contact Helen Brownlee helen.brownlee@housemark.co.uk to join or for more information.
